Threat Watch
Quickly assess your cybersecurity health with Threat Watch for actionable insights on compromised accounts and devices.
Visit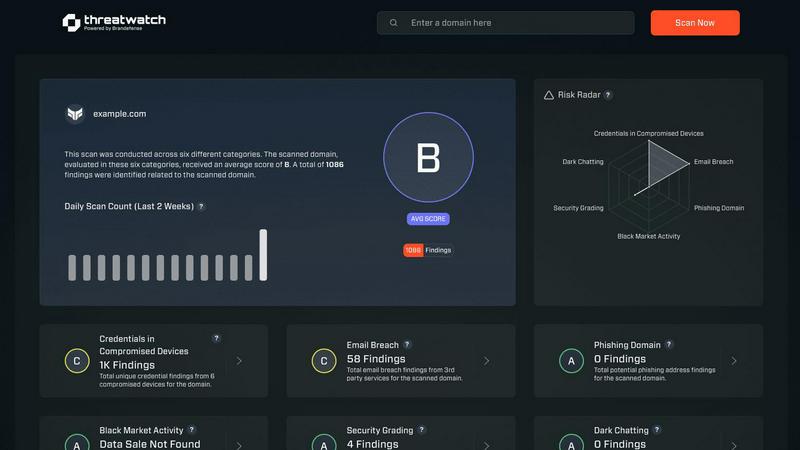
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform meticulously crafted to deliver organizations a comprehensive overview of their digital security posture. Unlike traditional security tools that operate in silos, Threat Watch integrates and analyzes data from a wide array of sources, providing a unified view of your external attack surface. This platform continuously scans your assets, vulnerabilities, and exposures, correlating information to present a definitive picture of your cyber health in real-time. Tailored for security teams, IT managers, and business leaders, Threat Watch automates critical assessments and gathers threat intelligence efficiently. By identifying hidden risks and allowing for prioritization of remediation efforts based on actual impact, organizations can rapidly mitigate threats. Its core value lies in transforming complex security data into a single source of truth, enabling proactive defenses and informed decision-making, ultimately safeguarding your organization's reputation, data, and operational integrity.
Features of Threat Watch
Comprehensive External Attack Surface Analysis
Threat Watch provides an in-depth analysis of your organization's external attack surface. By continuously scanning for vulnerabilities and assessing potential threats, it helps identify weaknesses before they can be exploited by malicious actors.
Automated Threat Intelligence Gathering
The platform automates the collection of critical threat intelligence data, allowing security teams to focus on remediation efforts rather than manual data collection. This efficiency ensures that teams are always aware of the latest threats impacting their assets.
Real-Time Risk Assessment
With Threat Watch, organizations gain access to real-time risk assessments that highlight vulnerabilities and exposures as they occur. This feature enables proactive responses to emerging threats, ensuring that security measures are always up-to-date and effective.
User-Friendly Dashboard
The intuitive dashboard of Threat Watch simplifies data interpretation, presenting complex security information in an easily digestible format. Users can quickly assess their cyber health, track remediation progress, and make informed decisions based on clear visualizations.
Use Cases of Threat Watch
Identifying Vulnerabilities in Real-Time
Organizations can utilize Threat Watch to continuously monitor their systems for vulnerabilities. This proactive approach allows security teams to address weaknesses as they arise, reducing the risk of data breaches.
Prioritizing Remediation Efforts
With its automated assessments, Threat Watch enables organizations to prioritize which vulnerabilities to address first based on their potential impact. This strategic focus on high-risk issues helps optimize resource allocation and enhance overall security.
Monitoring Dark Web Threats
Threat Watch allows organizations to monitor dark web content for any mention of compromised credentials or stolen data. This feature is crucial for taking preemptive action against potential breaches before they escalate.
Enhancing Incident Response Capabilities
By providing actionable insights and real-time data, Threat Watch enhances an organization's incident response capabilities. Security teams can quickly identify and respond to threats, minimizing damage and recovery time.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity concerned about its cybersecurity posture can leverage the platform for enhanced protection.
How does Threat Watch ensure data security?
Threat Watch employs robust encryption protocols and adheres to industry best practices to secure data both in transit and at rest. This commitment ensures that sensitive information remains protected from unauthorized access.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems. This compatibility allows organizations to enhance their current security infrastructure without significant overhauls.
Is training required to use Threat Watch?
While Threat Watch features a user-friendly interface, training sessions and resources are available to help users fully leverage the platform's capabilities. This ensures that organizations can maximize their investment in the tool effectively.
Explore more in this category:
Similar to Threat Watch
Decker
Decker is a deliverable operating system that helps consultants build, learn, and monetize their work through AI-powered workflows and a peer network.
BriskReach
BriskReach streamlines LinkedIn outreach for lead gen agencies, ensuring safe, effective campaigns with customizable messages and real-time replies.
PriceForge
PriceForge delivers real-time competitor pricing insights and automated updates, empowering B2B teams to stay ahead without the high costs.
AI Business Name Generator
Instantly create unique and memorable business names tailored for startups and brands with our free AI Business Name Generator.
AIHuntList
AIHuntList is your ultimate directory for discovering over 3000 AI tools across 200 categories, enhancing productivity and creativity.
Opal44
Opal44 explains your website traffic in plain English with AI insights from GA4.
Fusedash
Fusedash turns raw data into clear dashboards and charts for instant team insights.
finban
finban is your liquidity OS, giving you the cash clarity to make confident business decisions.