Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Pursuit
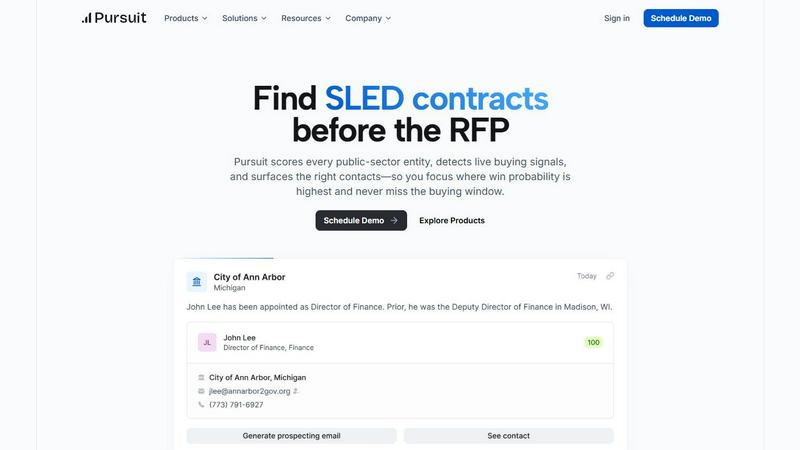
Pursuit helps you win SLED deals by surfacing opportunities long before the RFP.
Last updated: February 28, 2026
Threat Watch
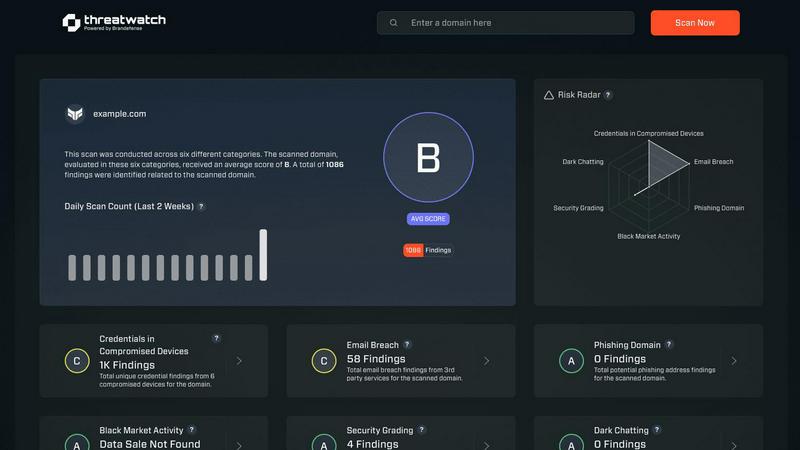
Quickly assess your cybersecurity health with Threat Watch for actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Detection
Pursuit's core engine scans and analyzes millions of data points from budget cycles, meeting minutes, and procurement portals to identify genuine buying intent long before an RFP is issued. It scores each SLED entity based on live signals, enabling teams to prioritize efforts on opportunities already moving toward a purchase, effectively capitalizing on critical budget windows and avoiding missed fiscal year cycles.
Entity & Contact Intelligence
The platform maintains a continuously enriched database of over 110,000 SLED entities, providing detailed organizational charts, verified contact information for decision-makers, incumbent vendor details, and historical contract data. This ensures teams have complete, accurate account context for every interaction, eliminating time-consuming manual research and keeping pace with frequent personnel changes in government.
Native CRM & Workflow Integrations
Pursuit offers bi-directional sync with major CRM platforms like Salesforce and HubSpot, ensuring signal and contact data flows automatically into sales teams' existing workflows. This seamless integration eliminates manual data entry, maintains a single source of truth, and enables features like prioritized call lists and alerts directly within reps' daily tools, driving adoption and efficiency.
Role-Specific Intelligence Portals
Beyond a generic database, Pursuit delivers tailored functionality for each persona. Account Executives get a Chrome extension for instant meeting prep, BDRs receive daily prioritized outreach lists, Marketing can build ABM campaigns on real signals, and Customer Success gets proactive renewal alerts. This ensures every team member operates on the same, relevant intelligence for their specific role.
Threat Watch
Comprehensive External Attack Surface Analysis
Threat Watch provides an in-depth analysis of your organization's external attack surface. By continuously scanning for vulnerabilities and assessing potential threats, it helps identify weaknesses before they can be exploited by malicious actors.
Automated Threat Intelligence Gathering
The platform automates the collection of critical threat intelligence data, allowing security teams to focus on remediation efforts rather than manual data collection. This efficiency ensures that teams are always aware of the latest threats impacting their assets.
Real-Time Risk Assessment
With Threat Watch, organizations gain access to real-time risk assessments that highlight vulnerabilities and exposures as they occur. This feature enables proactive responses to emerging threats, ensuring that security measures are always up-to-date and effective.
User-Friendly Dashboard
The intuitive dashboard of Threat Watch simplifies data interpretation, presenting complex security information in an easily digestible format. Users can quickly assess their cyber health, track remediation progress, and make informed decisions based on clear visualizations.
Use Cases
Pursuit
Accelerating New Business Pipeline
Sales Development Representatives and Account Executives use Pursuit's daily alerts on budget approvals, new initiatives, and contract expirations to identify and engage with in-market accounts. By focusing on scored, high-intent signals, teams can build a qualified pipeline 3x faster and achieve significantly higher cold-call conversion rates by leading with relevant insight.
Winning Competitive RFPs
For Account Executives, Pursuit provides critical competitive intelligence before an RFP drops. Knowing the incumbent vendor, contract value, procurement history, and the specific challenges an agency aims to solve allows teams to craft a compelling, tailored proposal and strategy, transforming them from outsiders to informed front-runners and improving win rates.
Running Targeted ABM Campaigns
Marketing teams leverage Pursuit to build precise Account-Based Marketing campaigns grounded in real buying signals. By syncing audiences of in-market entities to platforms like LinkedIn Ads, Marketo, or HubSpot, they can deliver hyper-relevant content based on budget cycles or new projects, lifting campaign conversion rates and supporting sales with warmed-up leads.
Proactive Customer Retention & Expansion
Customer Success managers configure alerts for key churn risks and renewal opportunities 90-180 days in advance. By monitoring signals like budget cuts, leadership changes, or competitor interest in their accounts, they can intervene proactively to secure renewals and identify expansion opportunities, protecting and growing existing contract revenue.
Threat Watch
Identifying Vulnerabilities in Real-Time
Organizations can utilize Threat Watch to continuously monitor their systems for vulnerabilities. This proactive approach allows security teams to address weaknesses as they arise, reducing the risk of data breaches.
Prioritizing Remediation Efforts
With its automated assessments, Threat Watch enables organizations to prioritize which vulnerabilities to address first based on their potential impact. This strategic focus on high-risk issues helps optimize resource allocation and enhance overall security.
Monitoring Dark Web Threats
Threat Watch allows organizations to monitor dark web content for any mention of compromised credentials or stolen data. This feature is crucial for taking preemptive action against potential breaches before they escalate.
Enhancing Incident Response Capabilities
By providing actionable insights and real-time data, Threat Watch enhances an organization's incident response capabilities. Security teams can quickly identify and respond to threats, minimizing damage and recovery time.
Overview
About Pursuit
Pursuit is the definitive pre-RFP intelligence platform for organizations selling to state, local, and education (SLED) government entities. It transforms the traditionally opaque and lengthy public sector sales cycle by surfacing actionable buying signals 6-18 months before a formal Request for Proposal (RFP) is published. The platform continuously monitors and scores over 110,000 public-sector entities, detecting critical intent from budget documents, council meetings, contract expirations, and leadership changes. This allows sales, marketing, and customer success teams to engage with precision and context, showing up as a knowledgeable partner rather than an outsider. By delivering curated, high-accuracy data on entities, key contacts, and live opportunities directly into existing CRM and sales workflows, Pursuit removes guesswork and administrative friction. The result is a shared intelligence ecosystem that empowers entire go-to-market teams to build a qualified pipeline earlier, improve win rates significantly, and secure public contracts with consistent success.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform meticulously crafted to deliver organizations a comprehensive overview of their digital security posture. Unlike traditional security tools that operate in silos, Threat Watch integrates and analyzes data from a wide array of sources, providing a unified view of your external attack surface. This platform continuously scans your assets, vulnerabilities, and exposures, correlating information to present a definitive picture of your cyber health in real-time. Tailored for security teams, IT managers, and business leaders, Threat Watch automates critical assessments and gathers threat intelligence efficiently. By identifying hidden risks and allowing for prioritization of remediation efforts based on actual impact, organizations can rapidly mitigate threats. Its core value lies in transforming complex security data into a single source of truth, enabling proactive defenses and informed decision-making, ultimately safeguarding your organization's reputation, data, and operational integrity.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit detect?
Pursuit detects a wide range of intent signals from public records, including budget appropriations for new projects, discussions in city council or school board meetings, expiring contracts with incumbent vendors, leadership changes in relevant departments, and the publication of RFIs or preliminary procurement documents. These signals indicate an entity is actively moving toward a purchase.
How does Pursuit ensure data accuracy and relevance?
The platform employs a multi-source verification process and continuous data enrichment to maintain a 94% accuracy rate. It cross-references official government databases, procurement portals, and public records, and its system is designed to update contact and organizational information as changes are published, ensuring teams always have current and reliable intelligence.
Can Pursuit integrate with our existing tech stack?
Yes, Pursuit offers native, bi-directional integrations with major CRM platforms including Salesforce and HubSpot. This allows for automatic syncing of account scores, contact details, and buying signals directly into your existing records. It also offers integrations for pushing audience data to marketing automation and advertising platforms.
Who within an organization is Pursuit designed for?
Pursuit is built for the entire go-to-market team targeting the SLED sector. This includes Sales Leaders and AEs for pipeline and deal strategy, BDRs for outbound prioritization, Marketing for targeted campaigns, Revenue Operations for data management, and Customer Success for renewal and retention efforts. Each persona receives a tailored view of the intelligence.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity concerned about its cybersecurity posture can leverage the platform for enhanced protection.
How does Threat Watch ensure data security?
Threat Watch employs robust encryption protocols and adheres to industry best practices to secure data both in transit and at rest. This commitment ensures that sensitive information remains protected from unauthorized access.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems. This compatibility allows organizations to enhance their current security infrastructure without significant overhauls.
Is training required to use Threat Watch?
While Threat Watch features a user-friendly interface, training sessions and resources are available to help users fully leverage the platform's capabilities. This ensures that organizations can maximize their investment in the tool effectively.
Alternatives
Pursuit Alternatives
Pursuit is a business intelligence platform designed specifically for companies selling to the public sector. It helps sales teams and government contractors identify and act on live opportunities by scoring entities, detecting buying signals, and providing detailed contact data. Users may explore alternatives for various reasons, such as budget constraints, a need for different feature sets, or a preference for a platform that integrates with a specific tech stack. Some may seek broader market intelligence tools, while others require more specialized functionality. When evaluating an alternative, consider its depth of public-sector data, the accuracy of its buying signals, and the quality of its contact intelligence. Seamless CRM integration and tools that save your team time, like browser extensions and automated alerts, are also critical for maximizing efficiency in a competitive landscape.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform designed to provide organizations with a clear and actionable view of their digital security posture. As a tool that focuses on evaluating external attack surfaces, it enables users to continuously monitor their cybersecurity health through automated assessments and real-time data analysis. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with existing systems and workflows. When exploring alternatives, it's essential to consider factors such as the comprehensiveness of threat detection, ease of integration, usability, and the ability to provide actionable insights that align with your organization's unique security needs.
