Karolium vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Karolium is a unified zero-code platform for building and customizing intelligent enterprise applications.
Last updated: February 28, 2026
Threat Watch
Quickly assess your cybersecurity health with Threat Watch for actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Platform
Karolium provides a single, code-free environment that combines iPaaS, aPaaS, oPaaS, and AIPaaS capabilities. This unified approach eliminates dependency on developer resources, allowing business users to visually design, integrate, and deploy sophisticated applications and workflows at remarkable speed. It enables boundless customization of both pre-packaged and user-composed modules, fostering true business agility without technical debt.
Pre-Composed Value-Chain Solutions
The platform offers a holistic suite of enterprise-grade, ready-to-deploy modules tailored for core business functions. These pre-composed solutions—such as Supplier Collaboration, Centralized Procurement, AI-Infused Demand Forecasting, and Unified Master Data Management—deliver immediate functionality. Organizations can implement these modules to address specific value-chain challenges rapidly, avoiding lengthy development cycles and costly custom builds from scratch.
Built-In Predictive & Prescriptive Analytics
Karolium is an enterprise intelligence platform with AI and analytics deeply embedded into its fabric. It offers built-in predictive and prescriptive solutions that transform raw data into actionable insights. This allows businesses to move beyond reactive operations, enabling applications that can forecast trends, recommend optimal actions, and drive measurable, data-informed outcomes across the organization.
Seamless Ecosystem Integration
Designed for the modern, heterogeneous IT landscape, Karolium focuses on seamless integration with both legacy systems and contemporary microservices-based applications. It facilitates real-time coordination and data flow across all layers of the application ecosystem without requiring complex point-to-point integrations, thereby enhancing collaboration and breaking down data silos.
Threat Watch
Comprehensive External Attack Surface Analysis
Threat Watch provides an in-depth analysis of your organization's external attack surface. By continuously scanning for vulnerabilities and assessing potential threats, it helps identify weaknesses before they can be exploited by malicious actors.
Automated Threat Intelligence Gathering
The platform automates the collection of critical threat intelligence data, allowing security teams to focus on remediation efforts rather than manual data collection. This efficiency ensures that teams are always aware of the latest threats impacting their assets.
Real-Time Risk Assessment
With Threat Watch, organizations gain access to real-time risk assessments that highlight vulnerabilities and exposures as they occur. This feature enables proactive responses to emerging threats, ensuring that security measures are always up-to-date and effective.
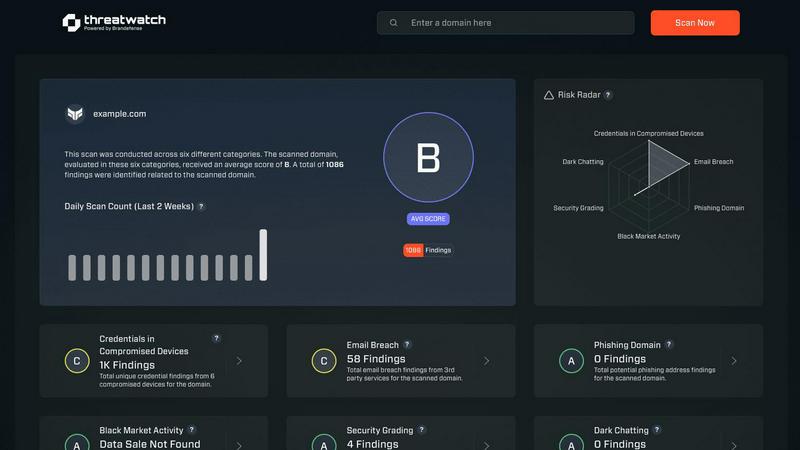
User-Friendly Dashboard
The intuitive dashboard of Threat Watch simplifies data interpretation, presenting complex security information in an easily digestible format. Users can quickly assess their cyber health, track remediation progress, and make informed decisions based on clear visualizations.
Use Cases
Karolium
Accelerating Digital Transformation Initiatives
Enterprises aiming to modernize their operations can use Karolium to rapidly build and deploy new applications that address evolving market demands. By leveraging the zero-code platform and pre-built modules, companies can accelerate their transformation roadmap, quickly launching intelligent solutions for areas like smart compliance or contract manufacturing without the traditional coding bottleneck.
Augmenting and Extending Legacy Systems
Organizations frustrated by the rigid limitations of their core ERP or CRM systems can use Karolium to augment these investments. The platform allows teams to build custom workflows, add customer-centric features, and extend functionalities to support unique business processes, all without the risk and cost of modifying the original vendor software.
Implementing AI-Driven Supply Chain Optimization
Businesses in manufacturing, logistics, or retail can deploy Karolium's value-chain solutions to create a more intelligent supply chain. By implementing modules for AI-infused demand forecasting, lead time prediction, and asset monitoring, they gain predictive insights that optimize inventory, improve supplier collaboration, and enhance overall operational resilience.
Creating Unified Operational Command Centers
Karolium enables the creation of tailored dashboards and applications that unify data from disparate sources—such as warehousing, procurement, and yard management systems. This provides leadership with a single pane of glass for real-time visibility, facilitating proactive decision-making and coordinated action across complex, multi-tiered operations.
Threat Watch
Identifying Vulnerabilities in Real-Time
Organizations can utilize Threat Watch to continuously monitor their systems for vulnerabilities. This proactive approach allows security teams to address weaknesses as they arise, reducing the risk of data breaches.
Prioritizing Remediation Efforts
With its automated assessments, Threat Watch enables organizations to prioritize which vulnerabilities to address first based on their potential impact. This strategic focus on high-risk issues helps optimize resource allocation and enhance overall security.
Monitoring Dark Web Threats
Threat Watch allows organizations to monitor dark web content for any mention of compromised credentials or stolen data. This feature is crucial for taking preemptive action against potential breaches before they escalate.
Enhancing Incident Response Capabilities
By providing actionable insights and real-time data, Threat Watch enhances an organization's incident response capabilities. Security teams can quickly identify and respond to threats, minimizing damage and recovery time.
Overview
About Karolium
Karolium is a next-generation, unified zero-code enterprise platform designed to accelerate digital transformation for modern businesses. It uniquely converges the capabilities of an integration platform (iPaaS), application platform (aPaaS), operations platform (oPaaS), and AI platform (AIPaaS) into a single, cohesive environment. This empowers organizations to rapidly build, extend, and customize intelligent business solutions without the complexities, costs, and delays of traditional software development. The platform is specifically engineered for enterprises seeking greater agility, efficiency, and intelligence from their existing software investments. By offering a library of ready-to-use, pre-composed modules and complete composability, Karolium allows businesses to augment their current application ecosystems and tailor workflows precisely to their needs. Its core value proposition lies in delivering technology and business solutions that bridge critical gaps in traditional systems—enabling real-time collaboration, proactive AI-driven decision-making, and seamless adaptation to market volatility, all while maximizing the value of legacy and modern software assets.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform meticulously crafted to deliver organizations a comprehensive overview of their digital security posture. Unlike traditional security tools that operate in silos, Threat Watch integrates and analyzes data from a wide array of sources, providing a unified view of your external attack surface. This platform continuously scans your assets, vulnerabilities, and exposures, correlating information to present a definitive picture of your cyber health in real-time. Tailored for security teams, IT managers, and business leaders, Threat Watch automates critical assessments and gathers threat intelligence efficiently. By identifying hidden risks and allowing for prioritization of remediation efforts based on actual impact, organizations can rapidly mitigate threats. Its core value lies in transforming complex security data into a single source of truth, enabling proactive defenses and informed decision-making, ultimately safeguarding your organization's reputation, data, and operational integrity.
Frequently Asked Questions
Karolium FAQ
What makes Karolium different from other low-code/no-code platforms?
Karolium is distinguished as a unified enterprise platform that converges integration, application development, operations, and AI capabilities into a single zero-code environment. Unlike generic tools, it offers pre-composed, industry-relevant value-chain solutions and is designed specifically for augmenting complex enterprise ecosystems. Its focus on delivering both technology enablers and ready-to-deploy business solutions for core functions like supply chain sets it apart.
Can Karolium integrate with our existing software investments?
Absolutely. Seamless integration is a cornerstone of the Karolium platform. It is architecturally designed to connect with and extend the functionality of both legacy systems and modern microservices applications. This allows you to enhance your current software portfolio without costly replacements or disruptive point-to-point integration projects, maximizing your existing IT investments.
Is Karolium suitable for businesses without AI expertise?
Yes. Karolium is built to democratize AI adoption. It provides built-in predictive and prescriptive analytics solutions within its modules, such as AI-infused demand forecasting. This allows organizations to leverage advanced AI capabilities through configurable, code-free applications, enabling tangible business improvements without requiring in-house data science teams or deep technical expertise.
How does the platform handle updates and new features?
Karolium is delivered as a managed PaaS-driven SaaS platform. This model ensures continuous access to the latest platform capabilities, security updates, and regular enhancements to its solution modules. The company commits to a roadmap featuring quarterly releases that include new value-chain modules and platform features, ensuring your solutions evolve with market demands.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity concerned about its cybersecurity posture can leverage the platform for enhanced protection.
How does Threat Watch ensure data security?
Threat Watch employs robust encryption protocols and adheres to industry best practices to secure data both in transit and at rest. This commitment ensures that sensitive information remains protected from unauthorized access.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems. This compatibility allows organizations to enhance their current security infrastructure without significant overhauls.
Is training required to use Threat Watch?
While Threat Watch features a user-friendly interface, training sessions and resources are available to help users fully leverage the platform's capabilities. This ensures that organizations can maximize their investment in the tool effectively.
Alternatives
Karolium Alternatives
Karolium is a unified zero-code platform in the development category, designed to help enterprises build AI-driven business applications rapidly. It emphasizes seamless integration, ready-to-use modules, and built-in analytics to accelerate digital transformation without traditional coding. Users may explore alternatives for various reasons, such as specific budget constraints, the need for different feature sets like advanced workflow automation, or platform requirements concerning scalability and niche integrations. The search often stems from finding the perfect balance between capability, cost, and long-term strategic fit. When evaluating alternatives, key considerations include the depth of AI and analytics tools, the true ease of use for your team, the robustness of integration capabilities with your current stack, and the total cost of ownership. The goal is to identify a platform that not only matches your immediate technical needs but also supports sustainable growth and innovation.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform designed to provide organizations with a clear and actionable view of their digital security posture. As a tool that focuses on evaluating external attack surfaces, it enables users to continuously monitor their cybersecurity health through automated assessments and real-time data analysis. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with existing systems and workflows. When exploring alternatives, it's essential to consider factors such as the comprehensiveness of threat detection, ease of integration, usability, and the ability to provide actionable insights that align with your organization's unique security needs.
