iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
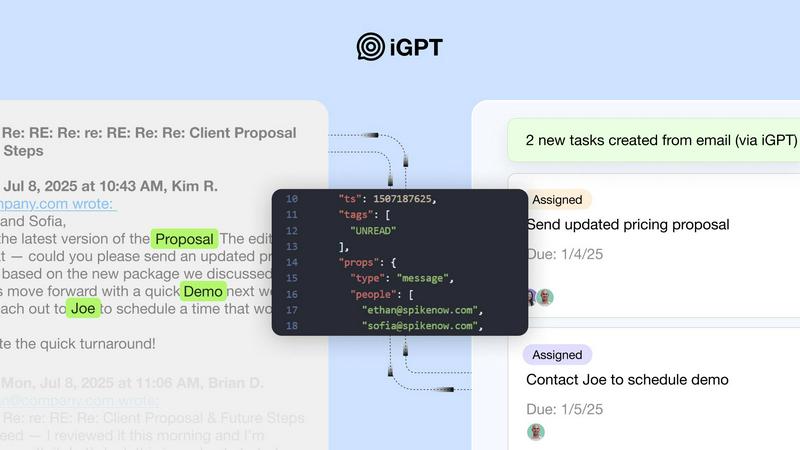
iGPT transforms email data into actionable insights through a secure API for seamless automation and context-aware.
Last updated: March 1, 2026
Threat Watch
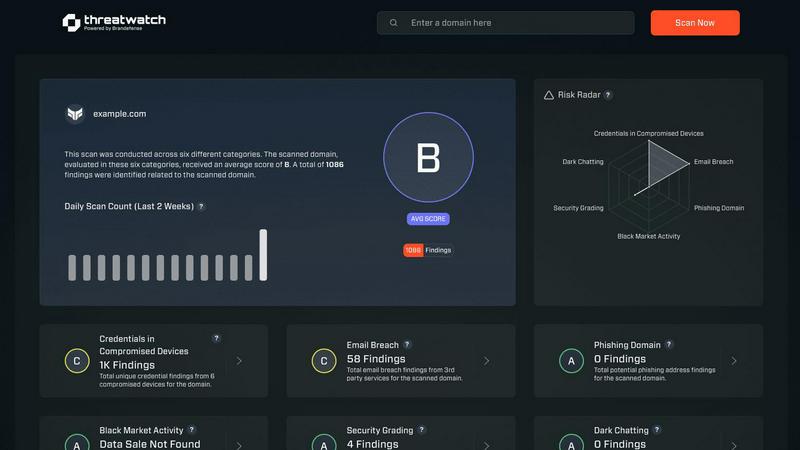
Quickly assess your cybersecurity health with Threat Watch for actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT provides an SDK and a live playground, allowing users to test requests and responses quickly. This feature simplifies the process of connecting to email sources and ensures a smooth onboarding experience.
Unified Endpoint
With iGPT, users can send a single request that runs retrieval, context shaping, and reasoning in one streamlined pipeline. This eliminates the need for multiple endpoints and enhances efficiency in accessing email data.
Contextual Responses
iGPT delivers responses that are ready for reasoning and automation, complete with citations to the original source. This feature ensures that users can trust the information while maintaining a clear link to its origin.
Continuous Data Indexing
The API continuously indexes new messages and attachments in real-time, ensuring that data and answers are always up-to-date. This feature is vital for organizations needing to act on the most current information available.
Threat Watch
Comprehensive External Attack Surface Analysis
Threat Watch provides an in-depth analysis of your organization's external attack surface. By continuously scanning for vulnerabilities and assessing potential threats, it helps identify weaknesses before they can be exploited by malicious actors.
Automated Threat Intelligence Gathering
The platform automates the collection of critical threat intelligence data, allowing security teams to focus on remediation efforts rather than manual data collection. This efficiency ensures that teams are always aware of the latest threats impacting their assets.
Real-Time Risk Assessment
With Threat Watch, organizations gain access to real-time risk assessments that highlight vulnerabilities and exposures as they occur. This feature enables proactive responses to emerging threats, ensuring that security measures are always up-to-date and effective.
User-Friendly Dashboard
The intuitive dashboard of Threat Watch simplifies data interpretation, presenting complex security information in an easily digestible format. Users can quickly assess their cyber health, track remediation progress, and make informed decisions based on clear visualizations.
Use Cases
iGPT
Email Assistants
Organizations can build intelligent agents that draft, prioritize, and take action on emails with full contextual understanding. This capability streamlines communication and reduces the time spent on manual tasks.
Workflow Automation
iGPT can transform email threads into actionable tasks, deadlines, and approvals, flagging items that may be stuck. This feature enhances overall workflow efficiency and ensures that critical tasks are not overlooked.
Support Copilots
iGPT enables businesses to reconstruct the entire customer story across lengthy email chains, attachments, and tone shifts. This functionality improves customer support by providing comprehensive context for agents.
Insights from Attachments
The API can summarize and extract insights from documents, invoices, contracts, and other files in relation to their corresponding email threads. This feature allows organizations to gain valuable insights without sifting through multiple documents.
Threat Watch
Identifying Vulnerabilities in Real-Time
Organizations can utilize Threat Watch to continuously monitor their systems for vulnerabilities. This proactive approach allows security teams to address weaknesses as they arise, reducing the risk of data breaches.
Prioritizing Remediation Efforts
With its automated assessments, Threat Watch enables organizations to prioritize which vulnerabilities to address first based on their potential impact. This strategic focus on high-risk issues helps optimize resource allocation and enhance overall security.
Monitoring Dark Web Threats
Threat Watch allows organizations to monitor dark web content for any mention of compromised credentials or stolen data. This feature is crucial for taking preemptive action against potential breaches before they escalate.
Enhancing Incident Response Capabilities
By providing actionable insights and real-time data, Threat Watch enhances an organization's incident response capabilities. Security teams can quickly identify and respond to threats, minimizing damage and recovery time.
Overview
About iGPT
iGPT is a cutting-edge email intelligence API designed to enhance the way enterprises manage and interpret email communication. It empowers organizations by transforming raw email conversations and attachments into actionable insights, enabling users to extract relevant information swiftly. This API serves as a secure and auditable gateway that seamlessly integrates with AI-powered systems, ensuring that data remains trustworthy and context-aware. With its robust enterprise-grade infrastructure, iGPT emphasizes security, offering end-to-end encryption, granular access controls, and comprehensive audit trails. It is particularly suited for businesses aiming to deploy intelligent agents that operate with confidence, ensuring compliance while maintaining user trust. By automating the retrieval and contextualization of email data, iGPT significantly improves productivity and decision-making across various workflows.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform meticulously crafted to deliver organizations a comprehensive overview of their digital security posture. Unlike traditional security tools that operate in silos, Threat Watch integrates and analyzes data from a wide array of sources, providing a unified view of your external attack surface. This platform continuously scans your assets, vulnerabilities, and exposures, correlating information to present a definitive picture of your cyber health in real-time. Tailored for security teams, IT managers, and business leaders, Threat Watch automates critical assessments and gathers threat intelligence efficiently. By identifying hidden risks and allowing for prioritization of remediation efforts based on actual impact, organizations can rapidly mitigate threats. Its core value lies in transforming complex security data into a single source of truth, enabling proactive defenses and informed decision-making, ultimately safeguarding your organization's reputation, data, and operational integrity.
Frequently Asked Questions
iGPT FAQ
How does iGPT ensure data security?
iGPT employs enterprise-grade security measures, including zero data retention, role-based access control, and full audit trails, ensuring that your data remains secure and under your control.
Can iGPT be integrated with existing systems?
Yes, iGPT offers an SDK and a unified endpoint, making it easy to integrate with existing systems and workflows, allowing businesses to leverage their email data seamlessly.
What types of email data can iGPT process?
iGPT can process a wide range of email data, including conversations, attachments, and associated metadata, transforming them into context-aware insights for better decision-making.
Is there a limit on data retrieval speed?
iGPT is optimized for speed, with retrieval times around 200 milliseconds and approximately 3 seconds to the first token across large datasets, ensuring efficient access to email information.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity concerned about its cybersecurity posture can leverage the platform for enhanced protection.
How does Threat Watch ensure data security?
Threat Watch employs robust encryption protocols and adheres to industry best practices to secure data both in transit and at rest. This commitment ensures that sensitive information remains protected from unauthorized access.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems. This compatibility allows organizations to enhance their current security infrastructure without significant overhauls.
Is training required to use Threat Watch?
While Threat Watch features a user-friendly interface, training sessions and resources are available to help users fully leverage the platform's capabilities. This ensures that organizations can maximize their investment in the tool effectively.
Alternatives
iGPT Alternatives
iGPT is an advanced email intelligence API that belongs to the business intelligence category. It empowers organizations to derive actionable insights from their email communications, making it an essential tool for enterprises looking to enhance decision-making and productivity. Users often seek alternatives to iGPT due to various reasons, including pricing concerns, feature sets that may not align with specific needs, or compatibility with existing platforms and workflows. When searching for an alternative, it is crucial to evaluate factors such as integration capabilities, security features, the comprehensiveness of insights, and the overall user experience. Additionally, understanding how well an alternative can adapt to evolving business requirements and support a seamless workflow is essential for making an informed choice.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform designed to provide organizations with a clear and actionable view of their digital security posture. As a tool that focuses on evaluating external attack surfaces, it enables users to continuously monitor their cybersecurity health through automated assessments and real-time data analysis. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with existing systems and workflows. When exploring alternatives, it's essential to consider factors such as the comprehensiveness of threat detection, ease of integration, usability, and the ability to provide actionable insights that align with your organization's unique security needs.
