Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Deeploy
Deeploy provides the essential governance to scale AI with confidence and control.
Last updated: March 1, 2026
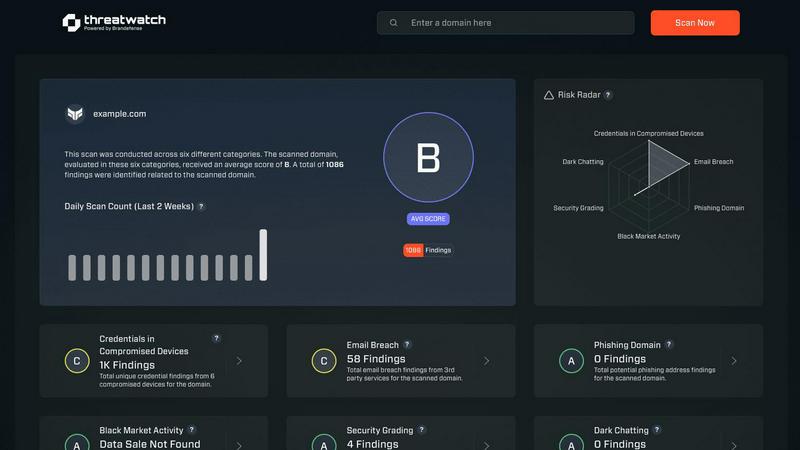
Threat Watch
Quickly assess your cybersecurity health with Threat Watch for actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Gain complete visibility and control from day one. Deeploy enables you to discover, onboard, and manage every AI system across your organization within a unified interface. It connects to any MLOps or GenAI platform, eliminating blind spots without forcing complex migrations. This centralized registry provides the foundational inventory and documentation necessary for effective governance and oversight.
Control Frameworks
Navigate AI regulations with guided simplicity. The platform allows you to implement default frameworks like ISO 42001 and NIST AI RMF or build custom ones tailored to your needs. You can classify AI system risk in minutes and establish clear accountability with structured approval processes. This turns complex compliance requirements into straightforward, manageable workflows.
Control Implementation
Translate policy into enforceable, engineer-friendly action. Deeploy automatically generates clear, actionable requirements for each AI system based on its risk classification. It accelerates compliance by up to 90% using pre-built templates and auto-collected evidence, and employs AI-powered assessments to handle repetitive governance tasks, ensuring policies are actually followed.
Real-Time Monitoring
Proactively prevent AI incidents and performance issues. Monitor model behavior, detect drift, and identify errors or anomalies in real-time before they impact users or create compliance risks. The system provides instant alerts and adds essential tracing and guardrails to protect LLM outputs, ensuring continuous, reliable operation.
Threat Watch
Comprehensive External Attack Surface Analysis
Threat Watch provides an in-depth analysis of your organization's external attack surface. By continuously scanning for vulnerabilities and assessing potential threats, it helps identify weaknesses before they can be exploited by malicious actors.
Automated Threat Intelligence Gathering
The platform automates the collection of critical threat intelligence data, allowing security teams to focus on remediation efforts rather than manual data collection. This efficiency ensures that teams are always aware of the latest threats impacting their assets.
Real-Time Risk Assessment
With Threat Watch, organizations gain access to real-time risk assessments that highlight vulnerabilities and exposures as they occur. This feature enables proactive responses to emerging threats, ensuring that security measures are always up-to-date and effective.
User-Friendly Dashboard
The intuitive dashboard of Threat Watch simplifies data interpretation, presenting complex security information in an easily digestible format. Users can quickly assess their cyber health, track remediation progress, and make informed decisions based on clear visualizations.
Use Cases
Deeploy
Centralized Governance for Multi-Vendor AI Estates
Organizations using AI models from various vendors and embedded across different departments can use Deeploy to create a single source of truth. It provides a central registry and oversight mechanism, bringing order to chaos, ensuring consistent policy application, and simplifying audit readiness across the entire fragmented AI landscape.
Accelerated Compliance with the EU AI Act
For companies operating in or selling to the EU, Deeploy streamlines adherence to stringent regulations. Its guided control frameworks help teams classify high-risk systems, implement necessary documentation and monitoring controls, and automatically collect evidence, significantly reducing the manual burden and time-to-compliance.
Enabling Responsible AI in Sensitive Industries
In sectors like healthcare or finance, explainability and human oversight are non-negotiable. Deeploy provides the critical feedback loops and real-time explainability features that allow experts to validate AI decisions, paving the way for safe and trusted AI adoption in environments where outcomes directly impact well-being.
Scaling AI Initiatives with Operational Confidence
Businesses looking to expand their AI portfolio can use Deeploy to establish a robust governance foundation. It reduces deployment time from weeks to hours, provides observability for both technical and non-technical teams, and implements proactive monitoring, allowing for faster, safer scaling of AI use cases.
Threat Watch
Identifying Vulnerabilities in Real-Time
Organizations can utilize Threat Watch to continuously monitor their systems for vulnerabilities. This proactive approach allows security teams to address weaknesses as they arise, reducing the risk of data breaches.
Prioritizing Remediation Efforts
With its automated assessments, Threat Watch enables organizations to prioritize which vulnerabilities to address first based on their potential impact. This strategic focus on high-risk issues helps optimize resource allocation and enhance overall security.
Monitoring Dark Web Threats
Threat Watch allows organizations to monitor dark web content for any mention of compromised credentials or stolen data. This feature is crucial for taking preemptive action against potential breaches before they escalate.
Enhancing Incident Response Capabilities
By providing actionable insights and real-time data, Threat Watch enhances an organization's incident response capabilities. Security teams can quickly identify and respond to threats, minimizing damage and recovery time.
Overview
About Deeploy
Deeploy is the essential governance infrastructure for organizations scaling artificial intelligence. In an era where AI is scattered across models, vendors, and embedded systems, Deeploy provides the centralized oversight needed to manage risk and maintain compliance. It is designed for enterprises running AI at scale, particularly those navigating complex regulations like the EU AI Act. The platform transforms a fragmented AI landscape into a controlled environment by offering complete visibility, actionable governance, and real-time monitoring from a single interface. Its core value proposition lies in eliminating blind spots and operational friction, allowing businesses to accelerate AI initiatives without sacrificing safety or control. By streamlining onboarding, enforcing compliance frameworks, and providing critical explainability, Deeploy empowers teams to deploy AI with confidence and build enduring trust in their AI-driven outcomes.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform meticulously crafted to deliver organizations a comprehensive overview of their digital security posture. Unlike traditional security tools that operate in silos, Threat Watch integrates and analyzes data from a wide array of sources, providing a unified view of your external attack surface. This platform continuously scans your assets, vulnerabilities, and exposures, correlating information to present a definitive picture of your cyber health in real-time. Tailored for security teams, IT managers, and business leaders, Threat Watch automates critical assessments and gathers threat intelligence efficiently. By identifying hidden risks and allowing for prioritization of remediation efforts based on actual impact, organizations can rapidly mitigate threats. Its core value lies in transforming complex security data into a single source of truth, enabling proactive defenses and informed decision-making, ultimately safeguarding your organization's reputation, data, and operational integrity.
Frequently Asked Questions
Deeploy FAQ
What types of AI systems can Deeploy manage?
Deeploy is designed as a universal governance layer. It can manage and monitor a wide variety of AI systems, including traditional machine learning models from MLOps platforms, generative AI applications from various vendors, and AI embedded in other software systems. Its flexible onboarding connects to your existing stack without requiring migration.
How does Deeploy help with AI explainability?
The platform provides built-in explainability features that help users understand how AI models arrive at their predictions or outputs. This transparency is crucial for debugging, building trust with stakeholders, and meeting regulatory requirements that mandate explainable AI, especially for high-risk applications.
Can we customize governance frameworks in Deeploy?
Yes. While Deeploy offers pre-configured, default frameworks based on major standards like ISO 42001, it also provides the flexibility to build and implement completely custom control frameworks. This allows you to tailor governance to your organization's specific internal policies, risk appetite, and industry requirements.
How does Deeploy's real-time monitoring work?
Deeploy continuously tracks the performance and behavior of AI models in production. It monitors for metrics like model drift, performance degradation, and anomalous outputs. The system triggers instant alerts when issues are detected, enabling teams to intervene before the problems affect end-users or lead to compliance violations.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity concerned about its cybersecurity posture can leverage the platform for enhanced protection.
How does Threat Watch ensure data security?
Threat Watch employs robust encryption protocols and adheres to industry best practices to secure data both in transit and at rest. This commitment ensures that sensitive information remains protected from unauthorized access.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems. This compatibility allows organizations to enhance their current security infrastructure without significant overhauls.
Is training required to use Threat Watch?
While Threat Watch features a user-friendly interface, training sessions and resources are available to help users fully leverage the platform's capabilities. This ensures that organizations can maximize their investment in the tool effectively.
Alternatives
Deeploy Alternatives
Deeploy is a specialized AI governance platform within the business intelligence category, designed to centralize oversight and ensure compliance for all organizational AI systems. It provides the critical framework needed to manage risk, explainability, and audit trails as AI adoption scales. Organizations may explore alternatives for various reasons, including budget constraints, specific feature requirements not covered by a single platform, or the need for a solution that integrates more tightly with their existing technical stack and vendor ecosystem. When evaluating an alternative, prioritize solutions that offer robust, actionable governance—not just monitoring. Look for capabilities in automated control enforcement, flexible regulatory framework support, and seamless integration without disruptive migration. The goal is to maintain compliance velocity and operational control as your AI portfolio evolves.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform designed to provide organizations with a clear and actionable view of their digital security posture. As a tool that focuses on evaluating external attack surfaces, it enables users to continuously monitor their cybersecurity health through automated assessments and real-time data analysis. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with existing systems and workflows. When exploring alternatives, it's essential to consider factors such as the comprehensiveness of threat detection, ease of integration, usability, and the ability to provide actionable insights that align with your organization's unique security needs.
