CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
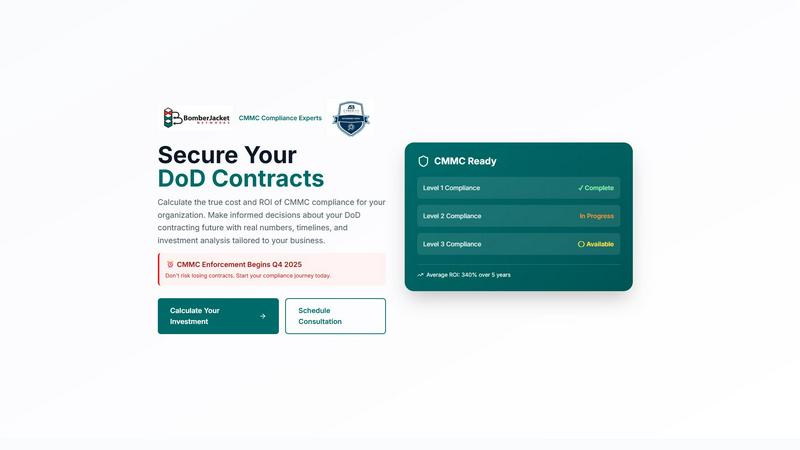
CMMC ROI
Calculate your CMMC compliance ROI to secure DoD contracts with confidence.
Last updated: March 1, 2026
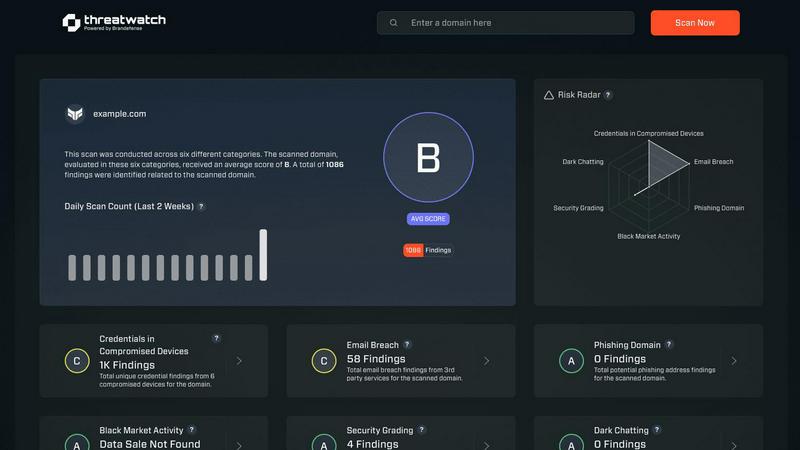
Threat Watch
Quickly assess your cybersecurity health with Threat Watch for actionable insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Personalized Investment Calculator
The core of the tool is a dynamic calculator that generates a tailored financial model based on your unique business profile. By adjusting inputs like company size, annual DoD revenue, required CMMC level, and current compliance status, you receive a precise range for your total 5-year investment, from implementation through maintenance and recertification. This eliminates guesswork and provides a concrete financial baseline for planning.
Comprehensive ROI & Payback Analysis
Go beyond simple cost reporting with a detailed analysis of your investment's return. The tool calculates your specific ROI percentage and identifies the exact month your investment will break even. It visually projects cumulative investment versus returns over a 5-year timeline, transforming compliance from an expense into a strategically timed investment with a clear path to profitability.
Contract Value at Risk Assessment
This critical feature quantifies the stark consequence of non-compliance. It calculates the total value of your DoD contracts that are 100% at risk without the required CMMC certification. This figure provides an undeniable financial imperative for action, making the business case for investment immediately clear to all stakeholders by highlighting the revenue in jeopardy.
Scenario Modeling with Pre-Built Examples
Jumpstart your planning with click-to-load scenarios for common contractor profiles, from a small FCI contractor to a large prime. These examples provide immediate context and benchmark data. For a perfect fit, you can then seamlessly input your own exact numbers to override the examples and generate a fully personalized forecast.
Threat Watch
Comprehensive External Attack Surface Analysis
Threat Watch provides an in-depth analysis of your organization's external attack surface. By continuously scanning for vulnerabilities and assessing potential threats, it helps identify weaknesses before they can be exploited by malicious actors.
Automated Threat Intelligence Gathering
The platform automates the collection of critical threat intelligence data, allowing security teams to focus on remediation efforts rather than manual data collection. This efficiency ensures that teams are always aware of the latest threats impacting their assets.
Real-Time Risk Assessment
With Threat Watch, organizations gain access to real-time risk assessments that highlight vulnerabilities and exposures as they occur. This feature enables proactive responses to emerging threats, ensuring that security measures are always up-to-date and effective.
User-Friendly Dashboard
The intuitive dashboard of Threat Watch simplifies data interpretation, presenting complex security information in an easily digestible format. Users can quickly assess their cyber health, track remediation progress, and make informed decisions based on clear visualizations.
Use Cases
CMMC ROI
Building an Executive Business Case
CFOs and business leaders use the tool to create a data-backed proposal for the board or ownership. The clear projections for cost, payback period, and ROI, coupled with the quantified risk of contract loss, transform the compliance discussion from a technical necessity into a strategic financial decision with defendable numbers.
Strategic Budget Planning and Justification
Compliance officers and IT directors leverage the detailed cost breakdowns—separating implementation, annual maintenance, and recertification costs—to build accurate, multi-year budgets. The tool justifies these line items by directly linking them to protected revenue and calculated returns, securing necessary funding.
Evaluating Compliance Progress Discounts
For organizations already on their CMMC journey, the tool applies meaningful discounts to the investment estimate based on current status. This allows teams "In Progress" or "Nearly Complete" to see the reduced financial outlay required to reach the finish line, validating prior efforts and refining the final budget.
Competitive Positioning and Bid Strategy
Business development and proposal teams use the ROI analysis to understand the competitive advantage conferred by certification. The tool's insight into increased win rates over non-certified competitors helps shape bid strategies and reinforces the value of being market-ready for post-2025 DoD solicitations.
Threat Watch
Identifying Vulnerabilities in Real-Time
Organizations can utilize Threat Watch to continuously monitor their systems for vulnerabilities. This proactive approach allows security teams to address weaknesses as they arise, reducing the risk of data breaches.
Prioritizing Remediation Efforts
With its automated assessments, Threat Watch enables organizations to prioritize which vulnerabilities to address first based on their potential impact. This strategic focus on high-risk issues helps optimize resource allocation and enhance overall security.
Monitoring Dark Web Threats
Threat Watch allows organizations to monitor dark web content for any mention of compromised credentials or stolen data. This feature is crucial for taking preemptive action against potential breaches before they escalate.
Enhancing Incident Response Capabilities
By providing actionable insights and real-time data, Threat Watch enhances an organization's incident response capabilities. Security teams can quickly identify and respond to threats, minimizing damage and recovery time.
Overview
About CMMC ROI
CMMC ROI is a strategic, data-driven financial planning tool designed exclusively for Department of Defense (DoD) contractors. It transforms the complex and often intimidating question of Cybersecurity Maturity Model Certification (CMMC) compliance from a vague cost center into a clear, quantifiable business investment. Built for business leaders, CFOs, and compliance officers, this tool moves organizations beyond rough estimates. By inputting specific company data—such as size, DoD revenue, and target CMMC level—users receive a personalized, multi-year financial forecast. This analysis details the true total cost of ownership, calculates a precise payback period, and projects the return on investment (ROI) for achieving and maintaining certification. Crucially, it quantifies the immense risk of inaction by showing the exact contract value at stake, while also modeling financial benefits like protected revenue, avoided breach costs, and competitive advantage. With CMMC enforcement beginning in Q4 2025, this tool empowers organizations to build a compelling, ROI-driven business case for compliance, securing their DoD contracting future with confidence and strategic clarity.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence platform meticulously crafted to deliver organizations a comprehensive overview of their digital security posture. Unlike traditional security tools that operate in silos, Threat Watch integrates and analyzes data from a wide array of sources, providing a unified view of your external attack surface. This platform continuously scans your assets, vulnerabilities, and exposures, correlating information to present a definitive picture of your cyber health in real-time. Tailored for security teams, IT managers, and business leaders, Threat Watch automates critical assessments and gathers threat intelligence efficiently. By identifying hidden risks and allowing for prioritization of remediation efforts based on actual impact, organizations can rapidly mitigate threats. Its core value lies in transforming complex security data into a single source of truth, enabling proactive defenses and informed decision-making, ultimately safeguarding your organization's reputation, data, and operational integrity.
Frequently Asked Questions
CMMC ROI FAQ
How accurate are the cost estimates provided?
The estimates are based on aggregated industry data and typical cost ranges for organizations of similar size and complexity pursuing specific CMMC levels. While they provide a highly reliable planning benchmark, your final costs may vary based on your specific environment, chosen solutions, and service providers. The tool is designed to give you a realistic financial framework.
What is included in the "Protected Value" for the ROI calculation?
The Protected Value is a conservative estimate of the financial benefit of certification. It primarily includes your total 5-year DoD contract revenue that would be at risk without CMMC. It also factors in an average cost avoidance for a potential data breach or false claims incident, which robust CMMC controls help prevent.
My company is already working on CMMC. Can the tool account for this?
Yes. The calculator includes a "Current Compliance Status" selector. Choosing "In Progress" applies a significant discount (e.g., 30%) to the implementation cost estimate, while "Nearly Complete" applies a larger discount (e.g., 60%). This reflects the reduced spend needed to complete your journey versus starting from scratch.
Why is the payback period often less than a year?
For most contractors, the value of the DoD contracts protected by certification is substantial and immediate upon enforcement. The tool models the investment cost against this large, at-risk revenue stream. Therefore, once certification is achieved and that revenue is secured, the initial investment is often recouped quickly, leading to a short payback period.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity concerned about its cybersecurity posture can leverage the platform for enhanced protection.
How does Threat Watch ensure data security?
Threat Watch employs robust encryption protocols and adheres to industry best practices to secure data both in transit and at rest. This commitment ensures that sensitive information remains protected from unauthorized access.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems. This compatibility allows organizations to enhance their current security infrastructure without significant overhauls.
Is training required to use Threat Watch?
While Threat Watch features a user-friendly interface, training sessions and resources are available to help users fully leverage the platform's capabilities. This ensures that organizations can maximize their investment in the tool effectively.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized business intelligence tool designed to provide DoD contractors with a precise, data-driven financial forecast for CMMC compliance. It transforms the complex question of cybersecurity investment into a clear strategic plan, quantifying costs, payback periods, and the return on investment needed to secure future contracts. Users may explore alternatives for various reasons, including budget constraints, a need for different feature sets, or a preference for a platform integrated with broader compliance or financial software. The search for the right tool is a critical step in strategic planning. When evaluating any solution, prioritize clarity and actionable insight. Look for a tool that delivers personalized, multi-year financial modeling, uses validated industry data, and clearly quantifies both the investment required and the tangible business value protected, such as contract revenue and avoided risk costs.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity intelligence platform designed to provide organizations with a clear and actionable view of their digital security posture. As a tool that focuses on evaluating external attack surfaces, it enables users to continuously monitor their cybersecurity health through automated assessments and real-time data analysis. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with existing systems and workflows. When exploring alternatives, it's essential to consider factors such as the comprehensiveness of threat detection, ease of integration, usability, and the ability to provide actionable insights that align with your organization's unique security needs.
