AutoPhish vs Decode This Text
Side-by-side comparison to help you choose the right AI tool.
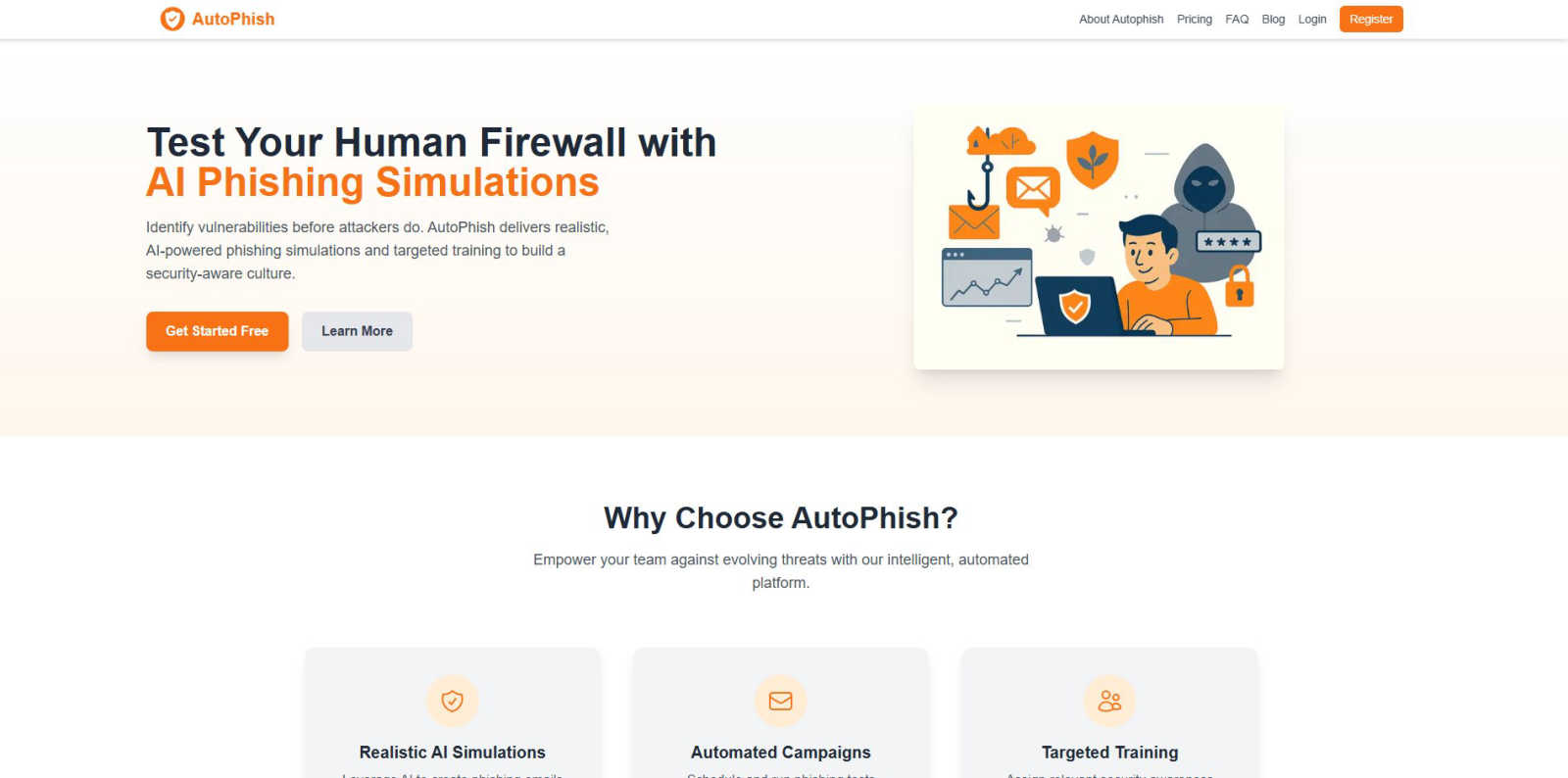
AutoPhish uses AI to run realistic phishing simulations and train your team against cyber threats.
Last updated: March 1, 2026
Decode This Text
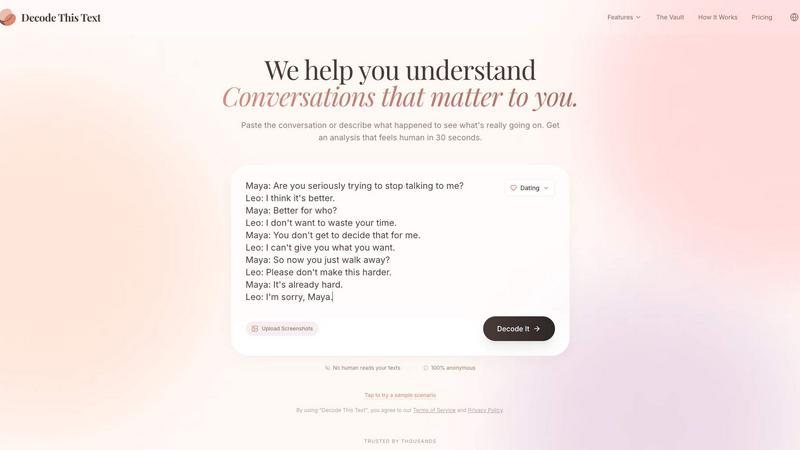
Decode This Text gives you human-like clarity on confusing conversations in just 30 seconds.
Last updated: February 28, 2026
Visual Comparison
AutoPhish
Decode This Text
Feature Comparison
AutoPhish
Realistic AI-Powered Simulations
AutoPhish leverages advanced artificial intelligence to generate phishing email simulations that are indistinguishable from genuine malicious campaigns. The AI tailors content, tone, and tactics to mimic threats specific to your industry, ensuring tests are relevant and challenging. This moves beyond basic template libraries to create a dynamic and unpredictable testing environment that truly prepares your team for the evolving tactics of real attackers.
Automated Phishing Campaigns
The platform allows for the complete automation of phishing simulation campaigns. Administrators can schedule tests to run consistently over time, ensuring ongoing vigilance without manual intervention. This automation saves significant administrative time and resources while guaranteeing that security awareness remains a continuous priority, not a one-time event, across the entire organization.
Targeted, Role-Based Training
Following each simulation, AutoPhish intelligently assigns follow-up security awareness training. This training is not one-size-fits-all; it is targeted based on the simulation results and the individual user's role within the company. Users who click a simulated link receive immediate, relevant education, making the learning experience direct, contextual, and far more effective than generic annual training modules.
Comprehensive Reporting & Analytics
AutoPhish provides advanced reporting dashboards that deliver clear, actionable insights into your organization's security posture. Track click-through rates, identify vulnerable users or departments, and monitor progress over time. These metrics allow security teams to measure ROI, demonstrate compliance needs, and make data-driven decisions to focus training efforts where they are needed most.
Decode This Text
Screenshot Analysis
Simply upload a photo of your chat conversation. The tool reads and analyzes the entire text exchange for you, eliminating the need to manually type out messages. This seamless feature saves time and ensures you capture every detail, from timestamps to emojis, for a complete and accurate interpretation of the interaction.
Tone & Intent Breakdown
Go beyond the words to understand the emotional temperature of a message. This feature measures whether the sender is being friendly, cold, sarcastic, or genuinely interested. It provides clear metrics on tone, effort, and intent, helping you avoid misinterpretation and see the true sentiment behind phrases like "I'll let you know."
Pattern Detection
The AI detects subtle behavioral cues that are easy to miss. It identifies patterns such as someone only messaging late at night, consistently avoiding direct questions, or gradually shortening their replies. This insight reveals underlying habits and intentions, providing context that explains confusing shifts in communication.
Smart Response Builder
Stuck on how to reply? This feature provides you with three tailored response options—calm, direct, or firm—based on the analysis of the situation. It helps you craft a confident reply that aligns with your goals, whether you need to set a boundary, seek clarity, or keep the conversation flowing smoothly.
Use Cases
AutoPhish
Proactive Security Posture Assessment
Organizations use AutoPhish to conduct regular, controlled phishing tests to identify vulnerabilities within their employee base before real attackers do. This proactive assessment provides a clear baseline understanding of risk, allowing security teams to quantify their human risk factor and prioritize security initiatives with concrete data.
Compliance & Regulatory Training
For businesses in regulated industries, AutoPhish serves as a tool to fulfill mandatory security awareness training requirements. The platform provides documented proof of ongoing employee education and testing, which is crucial for audits and demonstrating due diligence in protecting sensitive customer and corporate data.
Onboarding New Employees
Integrate AutoPhish into the employee onboarding process to establish security as a core company value from day one. New hires can receive a baseline simulation and introductory training, immediately integrating them into the company's culture of awareness and setting clear expectations for their role in cybersecurity.
Post-Incident Remediation & Training
Following a real security incident or breach, AutoPhish can be deployed to target specific departments or behaviors that were exploited. It allows for the creation of custom simulations that mirror the actual attack vector, providing critical, hands-on retraining to prevent repeat incidents and strengthen organizational resilience.
Decode This Text
Decoding Dating & Relationship Messages
Navigate the uncertainty of modern dating. Understand if a match is genuinely interested or fading away, interpret mixed signals after a great date, or decode the meaning behind sudden silence. Get clarity on intentions to decide your next move without endless anxiety or advice from friends.
Interpreting Professional Communication
Decipher ambiguous workplace messages with confidence. Understand if your boss's one-word email signifies anger, interpret the true meaning behind "we'll keep your resume on file," or learn how to say "no" professionally. Navigate office politics and communication with strategic insight.
Understanding Friends & Family Dynamics
Repair and maintain personal relationships. Figure out why a family group chat went silent after your message, understand a friend's distant tone, or interpret passive-aggressive comments. Gain an objective perspective to address issues without escalating conflict.
Preventing Regretful Messages
Act as a crucial buffer before you send an emotional text. Paste your drafted reply to get an analysis of how it might be perceived. This use case helps you avoid sending messages fueled by frustration or confusion that you might regret later, promoting more thoughtful communication.
Overview
About AutoPhish
AutoPhish is an AI-powered cybersecurity platform dedicated to transforming an organization's human firewall from a potential vulnerability into its strongest defense. It is designed for businesses of all sizes seeking a proactive, intelligent approach to security awareness. The core mission is to move beyond generic training by simulating the exact types of sophisticated phishing attacks that target your specific industry. The platform automates the entire lifecycle of security testing and education: from launching hyper-realistic, AI-crafted phishing simulations to delivering targeted training based on individual user performance. This continuous cycle of testing, learning, and reinforcing empowers employees with the practical skills needed to identify and respond to real threats. By providing clear insights into organizational vulnerabilities and automating remediation, AutoPhish offers a cost-effective, scalable solution to foster a pervasive culture of security awareness, significantly reducing the risk and impact of successful phishing attacks.
About Decode This Text
In a world where digital communication is often ambiguous, Decode This Text provides the clarity you need. It is an innovative AI-powered tool designed to decipher the true meaning behind confusing messages. Whether you're puzzling over a vague text from a date, a cryptic email from your boss, or a silent group chat with friends, this tool cuts through the uncertainty. You simply paste the conversation, upload a screenshot, or describe the context. Within 30 seconds, you receive a comprehensive, human-like analysis that breaks down the underlying intentions, emotional tone, and hidden patterns in the exchange. More than just an analyzer, it empowers you with actionable advice, suggesting the best ways to respond with confidence. Built with privacy at its core—no human ever reads your texts—it’s the trusted, anonymous reality check for anyone looking to improve their relationships, enhance communication skills, and eliminate the stress of overthinking every word.
Frequently Asked Questions
AutoPhish FAQ
How does AutoPhish ensure simulations are safe?
AutoPhish simulations are designed to be completely controlled and non-malicious. All links in simulated emails point to internal, secure AutoPhish servers for tracking and educational purposes only. No real malware is deployed, and no real user credentials or data are harvested. The platform operates with clear transparency to administrators.
What is required to get started with AutoPhish?
Getting started is a simple three-step process. First, you verify and connect your company domain to send simulation emails securely. Next, you configure your first campaign by choosing AI-generated templates, defining target employee groups, and setting a schedule. Finally, you launch the test and use the dashboard to analyze results and assign follow-up training.
Can we customize the phishing simulations?
Yes. While AutoPhish provides a library of AI-generated templates tailored to various industries, administrators have full control to customize email content, sender addresses, and landing pages. This allows you to create simulations that reflect brand-specific internal communications or replicate recent threat intelligence relevant to your sector.
How does the pricing work for growing teams?
AutoPhish offers scalable pricing tiers based primarily on the volume of simulated emails sent per month, not per user. This model, combined with unlimited campaigns and users on all plans, makes it cost-effective for organizations to grow. You can easily upgrade your plan as your testing needs expand, ensuring you only pay for the level of simulation activity you require.
Decode This Text FAQ
How does Decode This Text protect my privacy?
Your privacy is paramount. The analysis is performed entirely by AI algorithms. No human ever reads, reviews, or stores the text conversations or screenshots you submit. All interactions are 100% anonymous, ensuring your sensitive communications remain completely confidential.
What kind of input does the tool accept?
You can provide input in three flexible ways: by directly pasting the text of a conversation, by uploading a screenshot or photo of your chat, or by simply describing the situation and what was said. The AI is designed to work effectively with any of these formats to give you a clear analysis.
How accurate is the analysis?
The tool uses advanced natural language processing trained on vast datasets of human communication to identify tone, intent, and patterns. While it provides highly insightful and nuanced analysis that users describe as a "wise older sister," it is an AI guide. It's designed to offer a powerful external perspective to inform your decisions.
What do I get in the analysis report?
Your report includes a breakdown of the perceived emotional tone, the level of effort from the sender, and their likely intent. It also highlights any detected communication patterns and, most importantly, provides you with actionable, context-aware suggestions for how to craft an effective response.
Alternatives
AutoPhish Alternatives
AutoPhish is a specialized platform in the cybersecurity awareness category, using AI-driven phishing simulations and tailored training to help organizations build a human firewall. It automates the process of testing employee vigilance and educating teams on modern threats. Businesses often explore alternatives for various reasons. These can include budget constraints, the need for different feature sets like more granular reporting or third-party integrations, or a preference for a platform that aligns with a specific company size or existing tech stack. The search for the right fit is a common step in the procurement process. When evaluating options, focus on core capabilities. Key considerations should be the realism and adaptability of the simulated attacks, the quality and relevance of the accompanying training materials, the depth of actionable reporting, and the overall ease of use for administrators. The goal is to find a solution that seamlessly integrates ongoing security education into your company's culture.
Decode This Text Alternatives
Decode This Text is a productivity tool designed to bring clarity to confusing communications. It analyzes text from emails, messages, or conversations to reveal underlying intentions, emotional tone, and suggested responses, helping users navigate ambiguous interactions with confidence. People often seek alternatives for various practical reasons. This could be due to budget constraints, a need for different features like integration with specific platforms, or simply a preference for a different user interface or analysis style. Exploring options ensures you find a tool that aligns perfectly with your workflow and communication challenges. When evaluating other tools, consider what matters most for your daily use. Look at the depth and nuance of the analysis provided, the speed of response, ease of use, and data privacy policies. The right alternative should not only decode text but also fit seamlessly into your life, enhancing understanding without adding complexity.
